OKIOK’S GLOBAL OFFER
AVAILABLE SERVICES
A solid foundation. A unique approach. A comprehensive offering of innovative cyber security services, in all business sectors.
ACTIVITIES INTERVENTIONS
DELIVERABLES
SECURITY POSTURE
- Maturity Analysis
 In line with your strategic needs, OKIOK offers a simplified approach based on its method of key controls which allows to make an assessment of the current situation on the maturity and effectiveness of security controls in order to identify areas for improvement.
In line with your strategic needs, OKIOK offers a simplified approach based on its method of key controls which allows to make an assessment of the current situation on the maturity and effectiveness of security controls in order to identify areas for improvement. - Health Check
Security Audit In order to fully understand your cyber security status, OKIOK uses its key control method, aligned with the ISO 27002 standard, to analyze the maturity of controls and practices with maximum impact on risk.
In order to fully understand your cyber security status, OKIOK uses its key control method, aligned with the ISO 27002 standard, to analyze the maturity of controls and practices with maximum impact on risk. - Vulnerability
Assessment OKIOK uses proprietary methodology and state-of-the-art tools to identify vulnerabilities that could make IT services vulnerable to incidents and attacks.
OKIOK uses proprietary methodology and state-of-the-art tools to identify vulnerabilities that could make IT services vulnerable to incidents and attacks. - Penetration Testing
 Once vulnerabilities are identified in your IT services, OKIOK tests their exploitability with an arsenal of tools and advanced techniques applied to a multitude of attack vectors.
Once vulnerabilities are identified in your IT services, OKIOK tests their exploitability with an arsenal of tools and advanced techniques applied to a multitude of attack vectors. - Anti-Phishing Testing
 OKIOK offers a personalized phishing campaign service to identify weaknesses in employee habits and behavior.
OKIOK offers a personalized phishing campaign service to identify weaknesses in employee habits and behavior. - Risk Analysis
 Using OKIOK’s unique key control methodology, OKIOK experts proceed to risk identification, analysis and assessment or to a complete review of your overall risk management process according to the needs of your industry.
Using OKIOK’s unique key control methodology, OKIOK experts proceed to risk identification, analysis and assessment or to a complete review of your overall risk management process according to the needs of your industry.
ACTIVITIES INTERVENTIONS
- Vulnerabilities
- Gaps
- Recommendations
DELIVERABLES
GOVERNANCE
- Governance
Assessment OKIOK conducts an evaluation that takes in consideration your strategic directions and allows you to implement, enhance or optimize your cyber security governance framework.
OKIOK conducts an evaluation that takes in consideration your strategic directions and allows you to implement, enhance or optimize your cyber security governance framework. - Security Policy Review
 Along with the governance assessment and taking in consideration regulatory requirements, this review will position your company favorably on the market.
Along with the governance assessment and taking in consideration regulatory requirements, this review will position your company favorably on the market. - Data Classification
Data Categorisation Based on the three core principles of cyber security (Confidentiality, Integrity, Availability), OKIOK’s unique categorization approach helps determine the criticality of information assets, improves your risk management process, and facilitates your decision making in terms of computer data access.
Based on the three core principles of cyber security (Confidentiality, Integrity, Availability), OKIOK’s unique categorization approach helps determine the criticality of information assets, improves your risk management process, and facilitates your decision making in terms of computer data access.
- Normative and Regulatory Framework
- Roles and Responsibilities
- Security Policies
EXPERTISE
- Solution Design
 OKIOK is able to build solutions tailored to your organization’s needs: Developing a complete solution or integrating a component with an existing technology, OKIOK ensures an efficient and adapted intervention, focused on maximizing the capital invested.
OKIOK is able to build solutions tailored to your organization’s needs: Developing a complete solution or integrating a component with an existing technology, OKIOK ensures an efficient and adapted intervention, focused on maximizing the capital invested. - Solution
Implementation The implementation of new solutions is sometimes complex. OKIOK puts at your disposal its team of experts to accompany you and allow a better integration to ensure the success of your projects.
The implementation of new solutions is sometimes complex. OKIOK puts at your disposal its team of experts to accompany you and allow a better integration to ensure the success of your projects. - Coaching
 With a partnership approach that allows an increased flexibility and expertise, OKIOK helps you to establish your vision and implement your plan, and supports you in your daily activities.
With a partnership approach that allows an increased flexibility and expertise, OKIOK helps you to establish your vision and implement your plan, and supports you in your daily activities. - SDLC
 OKIOK offers a range of services as part of your Secure Software Development Lifecycle (SDLC) to help you avoid security problems and reduce remediation costs.
OKIOK offers a range of services as part of your Secure Software Development Lifecycle (SDLC) to help you avoid security problems and reduce remediation costs.
- Security Architecture
- Security Services
- Security Process
- Security Solutions
STRATEGIC CONSULTING
- Cloud Strategy
 The cloud option is inevitable, but how to integrate it into your current framework? OKIOK supports you in all stages of the implementation of the strategy: governance, business impact, evaluation process, service classes and evaluation of solutions.
The cloud option is inevitable, but how to integrate it into your current framework? OKIOK supports you in all stages of the implementation of the strategy: governance, business impact, evaluation process, service classes and evaluation of solutions. - Identity Governance
and Administration
(IGA) Whether it is for governance, maturity enhancement or process optimization of your IGA, OKIOK helps you understand the current situation, develops a target and designs and realizes your IGA program in order to ensure its success and the achievement of its objectives.
Whether it is for governance, maturity enhancement or process optimization of your IGA, OKIOK helps you understand the current situation, develops a target and designs and realizes your IGA program in order to ensure its success and the achievement of its objectives.
- Strategic Vision
COMPUTER FORENSICS
- Remediation
Incident Response OKIOK accompanies you when your IT environment is affected by an event attributable to a human or technical cause. OKIOK searches for the cause of the problem and makes the necessary patches. This can be complemented by thorough investigation and forensic expertise.
OKIOK accompanies you when your IT environment is affected by an event attributable to a human or technical cause. OKIOK searches for the cause of the problem and makes the necessary patches. This can be complemented by thorough investigation and forensic expertise. - Preliminary Analysis
 The purpose of this activity is to determine whether a file requires further analysis and whether the production of an expert report is necessary. It includes preparatory meetings, secured back-up copies, data retrieval and a quick search for traces or evidence.
The purpose of this activity is to determine whether a file requires further analysis and whether the production of an expert report is necessary. It includes preparatory meetings, secured back-up copies, data retrieval and a quick search for traces or evidence. - Expertise
 OKIOK starts the appraisal by seizing the affected equipment to make copies. The information relevant to the analysis is then extracted from the copies and analyzed using specialized tools to identify the cause of the incident or the perpetrator.
OKIOK starts the appraisal by seizing the affected equipment to make copies. The information relevant to the analysis is then extracted from the copies and analyzed using specialized tools to identify the cause of the incident or the perpetrator. - Anti-Forensics
Counter-Expertise This activity consists of reviewing an expertise carried out by an adversary party, in order to identify the questionable elements and to evaluate the quality of the evidence presented. OKIOK experts give their opinion and make recommendations or assumptions about the expertise.
This activity consists of reviewing an expertise carried out by an adversary party, in order to identify the questionable elements and to evaluate the quality of the evidence presented. OKIOK experts give their opinion and make recommendations or assumptions about the expertise. - Strategic Coaching
 OKIOK provides you with its team of experts in computer forensics. Whether it is advice on investigative strategy or litigation, accompanying the Court during interrogation, drafting of interrogations or pleadings, OKIOK can help you.
OKIOK provides you with its team of experts in computer forensics. Whether it is advice on investigative strategy or litigation, accompanying the Court during interrogation, drafting of interrogations or pleadings, OKIOK can help you. - eDiscovery
 OKIOK performs indexing, organizing, reviewing and managing electronic evidence using software specifically designed to assist lawyers and organizations in the management of electronic evidence and other digital aspects of judicial proceedings.
OKIOK performs indexing, organizing, reviewing and managing electronic evidence using software specifically designed to assist lawyers and organizations in the management of electronic evidence and other digital aspects of judicial proceedings.
- Legal Copies
- Expert Report
- Expert Witness
SECURITY PROGRAM
The security program is designed to define, plan and oversee all the activities required to enhance and maintain your security posture according with your current situation, regulatory framework and business priorities.
PREREQUISITE
- Security
Posture - Business
Vision - Regulatory and Normative Framework
OKIOK CYBER SECURITY ARCHITECTURE

- Business Goals
- Policies and Standards
- Legal and Regulatory Card
- Risk Management

PEOPLE

process

TECHNOLOGY
Reliability Rating
SSDLC
Information
Awareness and Training
Access management
Applications
Dotation
Threat Management
Infrastructure
Arrival – Departure
Incident Management
Network
Vulnerability Management
Specific Technology
Metrics – Indicators – Dashboard
Change Management
CAPTURE THE VISION
Workshops with representatives from different business areas are held to understand your priorities and strategic directions. The results are combined with a reading of your security posture and your regulatory requirements to allow OKIOK to produce initiatives aligned with your business priorities.
ELABORATION OF INITIATIVES
Based on the results of the previous steps, OKIOK develops a set of initiatives based on the OKIOK security architecture (ASO). A categorization of initiatives along three axes (governance, structural and tactical) is then carried out in order to optimize the development of the security program.
PRIORIZATION
A prioritization of the initiatives is carried out according to their risk reduction impact in relation to the cost and the complexity of implementation, making possible the determination of an optimal sequence of implementation, developped over the duration of the program.









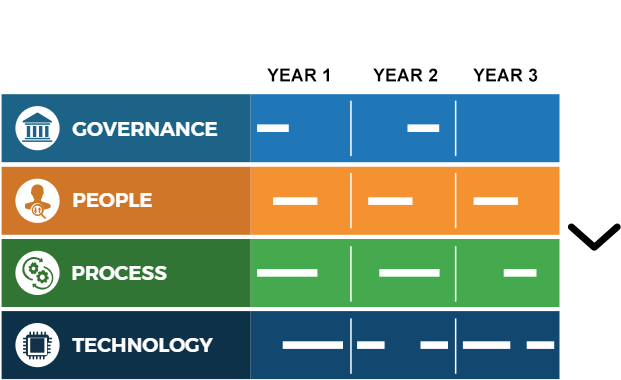

 GOVERNANCE
GOVERNANCE PEOPLE
PEOPLE PROCESS
PROCESS TECHNOLOGY
TECHNOLOGY




